Security Architecture as System Enforcement
Energy, Defence, and the Reinforcement of System Power
Keynote
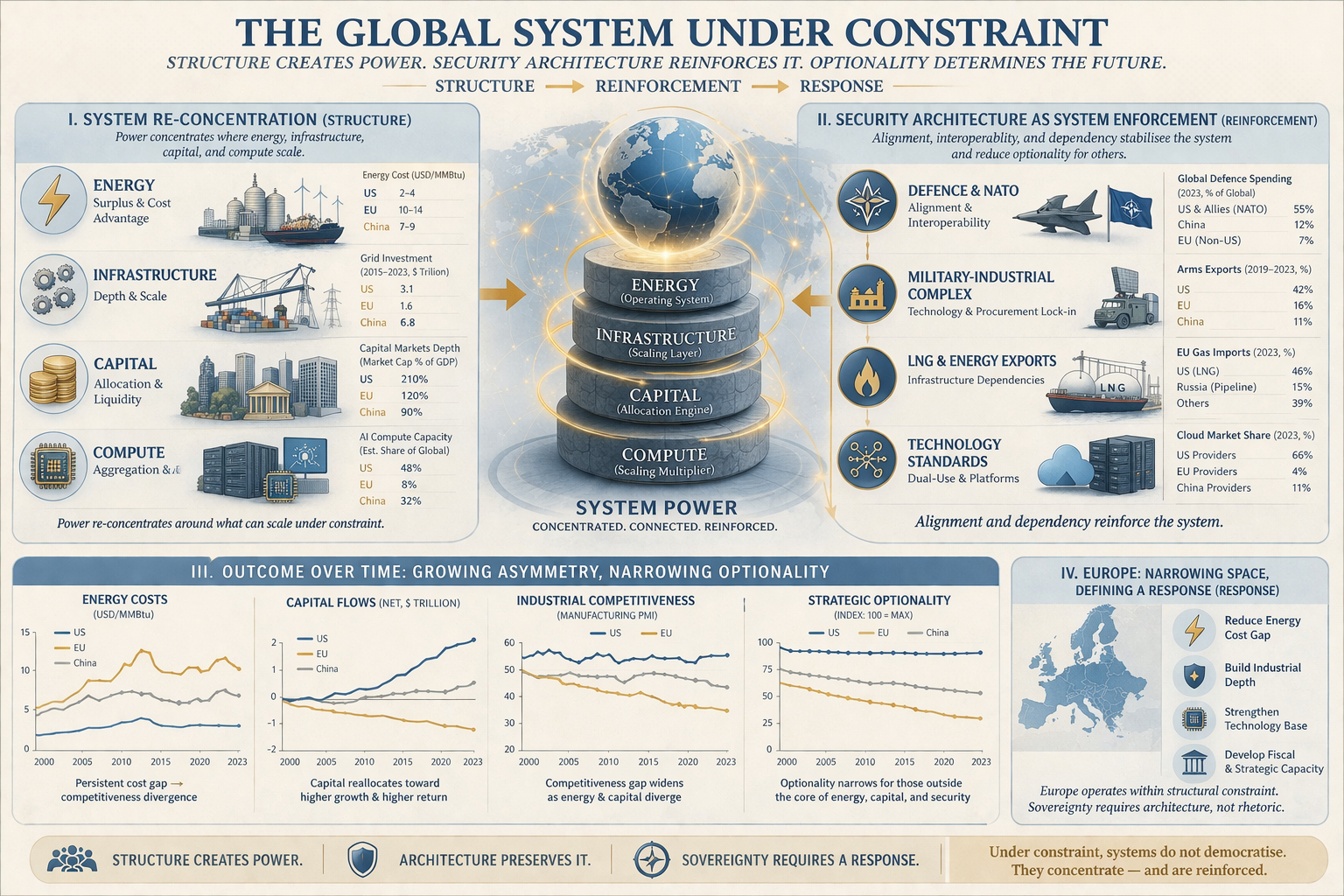
The global system is not only structured by energy, infrastructure, capital, and compute.
It is stabilised and reinforced by security architecture.
In an Energy-Bound System, power does not rely on
market dynamics alone.
It is embedded within a framework of:
defence alignment
industrial integration
technological interoperability
and strategic dependency
Security is not external to the system.
It is part of how the system holds.
System Navigation
This article extends:
- System Re-Concentration
- From Petrodollar to Infrastructure Currency - War, energy systems, and the reconfiguration of monetary power
- Security Architecture as System Enforcement (this article)- Energy, Defence, and the Reinforcement of System Power
- LNG, NATO, and the Enforcement of System Power - Energy Flows, Security Architecture, and the Financial Infrastructure of Control
- Defense Is Monetary Power: From Petrodollar to Digital Dollar - How the Dollar System Evolved from Energy and Security to Digital Infrastructure
- Monetary Sovereignty in an Energy-Bound System - Currency, Capital, and Control Under Structural Constraint
- Energy
Constraint and the Monetary Ceiling -How persistent marginal energy
disadvantage translates into currency pressure.
- Infrastructure Currency Doctrine
- Monetary Sovereignty and the New Monetary Cold War - Energy, Infrastructure, and the Struggle for System Control
- Monetary Power
- Energy, industry, infrastructure, geopolitics.
- Global Energy Flows and Trade Dependencies - How energy movement structures global power and dependence
- Energy as the Operating System of Power _Why energy defines the structure, limits, and distribution of modern power
- Energy Sovereignty as System Control - Power, Capacity, and Agency in an Energy-Bound World]
- Energy as the Operating System of Power — G2 Comparative - How the United States, China, and Europe express power under energy constraint
I. From Structure to Enforcement
The re-concentration of power follows a clear structural logic:
Energy → Infrastructure → Capital → Compute
But structure alone does not guarantee stability.
Under conditions of constraint, systems require reinforcement mechanisms.
This reinforcement is provided by:
security architecture
II. Security as Alignment Mechanism
Security frameworks operate as more than defence arrangements.
They function as systems of:
alignment
coordination
and constraint
Allied security structures reduce strategic uncertainty.
But they also:
shape procurement decisions
define interoperability standards
and anchor long-term technological pathways
Security, in this sense, is not neutral.
It is structuring.
III. Defence Systems and Industrial Integration
Modern defence systems are deeply integrated with industrial and technological ecosystems.
Procurement is not a one-off transaction.
It creates:
long-term maintenance dependencies
software and systems integration requirements
supply chain alignment
training and operational standardisation
Over time, this produces:
industrial and technological lock-in
This lock-in is not imposed externally.
It emerges from the logic of interoperability and system efficiency.
IV. NATO and System Coherence
Security alliances provide:
collective defence
strategic coordination
operational integration
But they also create:
shared standards
shared technologies
and shared dependencies
Within such frameworks:
defence procurement aligns
technological ecosystems converge
and industrial pathways narrow
This produces system coherence.
But coherence under constraint reduces optionality.
V. Credibility and System Asymmetry
Security architecture operates not only through alignment and integration, but through:
credibility
Credibility reduces uncertainty.
It stabilises expectations across:
- allied systems
- capital markets
- and strategic actors
It signals that the system will:
- hold
- respond
- and enforce alignment when required
However, credibility does not require symmetry.
Under conditions of constraint, systems prioritise:
coherence over balance
This can manifest as increasing asymmetry within alliances.
- burden-sharing adjusts
- procurement patterns concentrate
- energy and technology dependencies deepen
These shifts may appear, at the relationship level, as tension or imbalance.
At the system level, they reflect:
the reinforcement of hierarchy
A system can therefore remain credible—even as internal relationships become more asymmetric.
System credibility does not require relational symmetry.
VI. Energy Dependence and Infrastructure Lock-In
Energy systems are central to this dynamic.
The shift toward:
LNG infrastructure
flexible supply chains
and maritime energy flows
has reshaped energy dependency patterns.
Infrastructure investments in:
terminals
regasification
transport
create long-duration commitments.
These are not easily reversible.
They embed:
structural energy relationships
Energy supply is therefore not only economic.
It is system-defining.
VII. Technology, Compute, and Dual-Use Systems
The boundary between defence and civilian technology has eroded.
Key domains:
semiconductors
cloud infrastructure
artificial intelligence
communications systems
operate across both layers.
Security-driven investment accelerates:
technological scaling
platform consolidation
ecosystem dominance
This reinforces the concentration dynamics identified in:
VIII. Capital Flows and Strategic Alignment
Security architecture also shapes capital allocation.
Allied systems tend to exhibit:
lower perceived risk
higher capital inflows
deeper financial integration
External creditors and partners—
including sovereign capital from energy-exporting regions and industrial
powers—
interact with this system through:
infrastructure investment
financial markets
and technology deployment
These flows do not destabilise the system.
They often reinforce its core.
IX. Europe Reframed
Europe’s position within this system must be understood accordingly.
Europe is not simply:
constrained by energy
limited by policy
or delayed by institutions
It is:
embedded within a security, energy, and technological architecture that shapes its strategic space
This architecture provides:
stability
protection
and integration
But under constraint, it also:
limits divergence
shapes dependency
and narrows optionality
X. The System Logic
The global system is not maintained by market forces alone.
It is stabilised through the interaction of:
energy systems
industrial capacity
financial structures
technological platforms
and security architecture
Together, these form:
a coherent system of power
XI. Conclusion — Reinforcement, Not Neutrality
The current global order is not simply evolving through competition.
It is being:
structured
reinforced
and stabilised
Security architecture is central to this process.
It aligns systems.
It integrates industries.
It anchors dependencies.
Under constraint, power does not only concentrate.
It is reinforced.
Closing
The system does not rely on equilibrium.
It relies on alignment.
And alignment, once established, is difficult to unwind.
Next in the Series
→ From system structure and enforcement
→ to regional response:
**From Constraint to Sovereignty — A European Architecture
Reading Tree — System Power in an Energy-Bound World
From Structure to Reinforcement to Sovereignty
I. SYSTEM STRUCTURE
How power is organised
→ System Re-Concentration (this article) The global system is not fragmenting—it is re-concentrating around energy, infrastructure, capital, and compute.
System Reading Path
This sequence follows the full system logic:
Structure → Reinforcement → Consequence → Response
It is designed to move from global system dynamics to regional strategic positioning.
Supporting layers:
→ **Energy Systems and the Tech War How energy and compute define technological power
→ **Chokepoints Under Compression Control points and bottlenecks in a constrained system
→ **Energy Shock Transmission Chain How energy shocks propagate through the system
→ **The Energy J-Curve Why transition increases instability before stabilising
- US Energy and Monetary Power
- System Reconcentration
- Europe & Russia
- US Energy Abundance
- Global System Power Comparative Architecture
- China Industrial System
- China Technology & Energy Transition
- Energy Leverage
- The Global Energy Paradigm Shift
Global Energy System Transitiion]
II. SYSTEM CONSEQUENCE
How constraint transmits into regional outcomes
→ Energy Constraint and the Monetary Ceiling How energy cost divergence becomes monetary constraint
→ Execution Under Compression Why institutional latency amplifies structural disadvantage
III. SYSTEM RESPONSE
How sovereignty must be redefined under constraint
→ **From Constraint to Sovereignty — A European Architecture How Europe can reorganise under structural constraint